In the rapidly evolving landscape of mobile cybersecurity, the DarkSword Attack stands out as one of the most advanced and insidious threats targeting iPhone users today. Discovered in early March 2026 by researchers at Google Threat Intelligence Group, Lookout Threat Labs, and iVerify, this full-chain exploit kit represents a seamless blend of zero-click and drive-by delivery mechanisms specifically engineered for devices running iOS 18.4 through 18.7. Unlike traditional malware that requires user interaction such as downloading apps or clicking links, DarkSword operates silently through compromised legitimate websites, enabling attackers to achieve complete device compromise without any visible indicators. Fileless and entirely JavaScript-based, it leverages a chain of six vulnerabilities—including multiple zero-days such as CVE-2026-20700 (a PAC bypass in dyld) and CVE-2025-43529 (a use-after-free in JavaScriptCore)—to escape browser sandboxes and escalate to kernel-level privileges. Developed and deployed primarily by threat actors like UNC6353 (a suspected Russian espionage group), alongside commercial surveillance vendors, DarkSword has already targeted users in Ukraine, Saudi Arabia, Turkey, and Malaysia, underscoring its proliferation across nation-state and financially motivated campaigns. This exploit kit not only shatters the long-held perception of iOS as an impregnable fortress but also signals a new era where everyday web browsing on Safari can lead to total data exposure.
At its core, the DarkSword Attack employs the classic yet highly effective watering hole technique, turning trusted websites into silent infection vectors. Victims are infected simply by visiting compromised legitimate sites—such as Ukrainian news portals like novosti.dn[.]ua or government resources like 7aac.gov[.]ua—via the Safari browser on their iPhones. Attackers inject a malicious <iframe> or <script> tag (often loading from domains like static.cdncounter[.]net) that automatically triggers a loader script (rce_loader.js) upon page load. This process fingerprints the device’s iOS version and user agent, serving version-specific exploits while redirecting non-targets or Chrome users (via the x-safari-https handler) to benign content to avoid suspicion. No clicks, no downloads—just passive browsing on a site you might visit daily for news or services. The chain begins in the WebContent process, using obfuscated JavaScript to bypass detection, and sets session storage keys (like uid) to prevent re-exploitation.
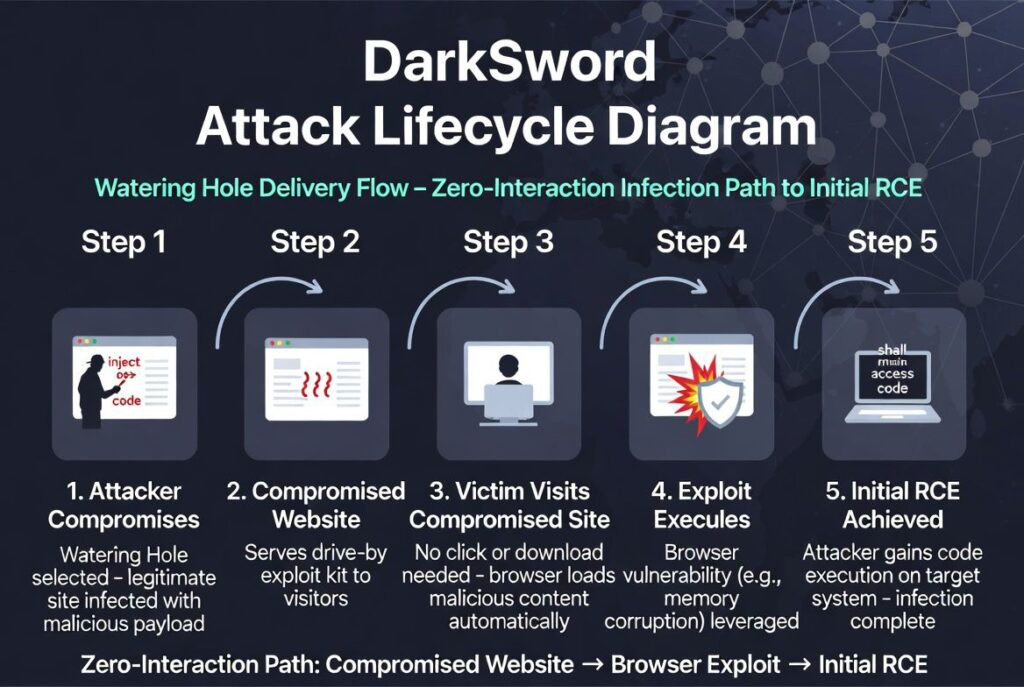
This drive-by method makes DarkSword exceptionally dangerous for tech-savvy users who rely on Safari for secure browsing, as it exploits the very trust we place in everyday web destinations.
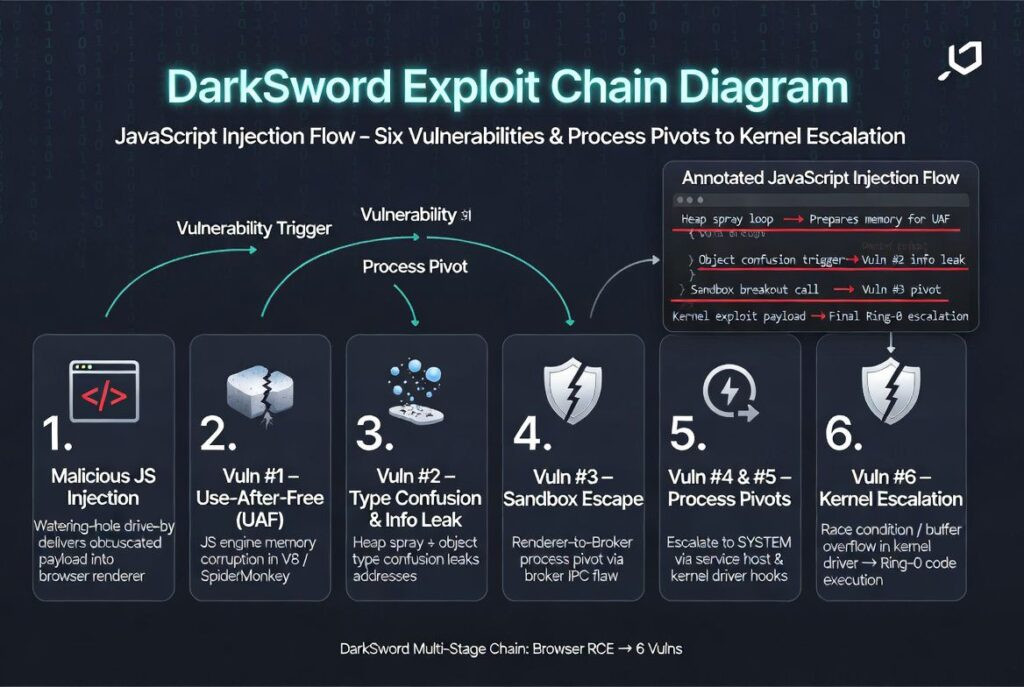
Diving deeper into the technical architecture reveals why DarkSword is considered a masterpiece of exploit engineering. The six-vulnerability chain starts with remote code execution (RCE) in Safari’s JavaScriptCore engine: for iOS 18.4–18.5, it abuses CVE-2025-31277 (JIT type confusion), while iOS 18.6–18.7 variants leverage CVE-2025-43529 for garbage collection flaws, building powerful addrof and fakeobj primitives despite mitigations like TPRO and PAC. From there, a WebContent sandbox escape pivots to the GPU process via CVE-2025-14174 (ANGLE out-of-bounds memory corruption using WebGL/WebGPU). A subsequent kernel-level pivot to the mediaplaybackd daemon exploits CVE-2025-43510 (XNU copy-on-write bug), loading the full JavaScriptCore runtime for further execution. Finally, local privilege escalation to kernel read/write capabilities is achieved through CVE-2025-43520 (XNU VFS race condition) and CVE-2026-20700 (dyld memory corruption), enabling arbitrary memory manipulation and sandbox modifications. All stages remain purely in-memory and JavaScript-driven, with modules like sbx0_main_18.4.js, pe_main.js, and custom injectors force-loading payloads into privileged daemons such as configd, wifid, securityd, and UserEventAgent—before culminating in SpringBoard injection. This fileless approach evades traditional antivirus entirely, as no binaries touch disk until the fleeting exfiltration stage.
What truly sets DarkSword apart is its ruthless hit-and-run operational model, optimized for speed and stealth rather than long-term persistence. Once kernel privileges are secured, the orchestrator (pe_main.js) deploys specialized modules—codenamed GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER—that rapidly stage and exfiltrate a treasure trove of sensitive data over HTTPS to C2 servers like sqwas.shapelie[.]com. Targets include crypto wallets (scanning for Coinbase, MetaMask, Binance, Ledger, and more), iMessages/SMS, photos, keychain passwords, WiFi credentials (tagged “DarkSword-WIFI-DUMP”), Safari history, iCloud data, health records, and even Telegram/WhatsApp databases. The entire operation completes in seconds to minutes: data is dumped to temporary /tmp paths with permissive permissions, uploaded via custom file downloader implants, and then meticulously wiped—deleting crash logs from DiagnosticReports directories, staged files, and any forensic traces to leave the device appearing pristine. This ephemeral nature not only minimizes detection windows but also aligns with financially motivated or espionage goals, allowing attackers to harvest crypto assets or intelligence before vanishing. The clean exit, combined with anti-debugging and conditional iOS version checks, makes forensic recovery extremely challenging even for advanced analysts.
Protecting against DarkSword demands proactive, layered defenses in an era where browser-based attacks bypass traditional safeguards. The most critical step is immediately updating to iOS 26.3 or newer, as Apple has patched all six vulnerabilities across incremental releases (iOS 18.6/18.7.x for early RCEs, culminating in 26.3 for the final PAC bypass). For high-risk users—journalists, activists, or those in targeted regions—enabling Lockdown Mode provides an additional barrier by restricting WebGL, JIT compilation, and certain Safari features that DarkSword relies upon. Beyond updates, practice vigilant web hygiene: avoid clicking unverified links even on familiar sites, use content blockers or alternative browsers where possible, and monitor for unusual battery drain or crashes that could signal exploitation attempts. Organizations should leverage enterprise tools like Google Safe Browsing blocklists for the known IOC domains and conduct regular device audits. While no single precaution eliminates every risk in this watering-hole landscape, staying patched and informed remains your strongest shield against this evolving iOS threat. Stay vigilant—the next generation of mobile exploits is already here.
Exploit Chain & Privilege Escalation
DarkSword chains six vulnerabilities (including at least three zero-days patched by Apple, such as CVE-2026-20700, CVE-2025-43529, CVE-2025-14174) to achieve full compromise:
- Initial RCE in Safari/WebContent via malicious JavaScript.
- Sandbox escape from WebContent.
- Injection into mediaplaybackd using WebGPU.
- Kernel read/write primitives. 5–6. Further pivots to bypass sandbox restrictions and access privileged filesystem areas.
This enables privileged code execution without user interaction.
Post-Exploitation & Data Theft
- Main orchestrator: pe_main.js (runs in mediaplaybackd).
- Force-loads JavaScriptCore + custom payloads into key system services: configd, wifid, securityd, UserEventAgent.
- Stages sensitive data.
- Final injection into Springboard for exfiltration to a C2 server.
- Hit-and-run style: Collects/exfiltrates data in minutes (or seconds), cleans up staged files, and exits cleanly → short dwell time, low detection chance.
Exfiltrated Data
DarkSword steals a wide range of sensitive information, including:
- Unique device identifiers
- SMS / iMessage
- Call history
- Address book / contacts
- WiFi configurations and passwords
- Safari history, cookies, bookmarks
- Location & location history
- Notes, Calendar, Health data
- Photos, screenshots
- iCloud Drive / iCloud content
- Cellular/SIM info
- Emails
- Installed app list
- Saved passwords / keychain
- Telegram & WhatsApp message history
- Cryptocurrency-related data: Targets wallets and exchanges like Coinbase, Binance, Kraken, Kucoin, OKX, Mexc, Ledger, Trezor, Metamask, Exodus, Uniswap, Phantom, Gnosis Safe, etc.
Appendix: IoCs
Network IoCs
static.cdncounter[.]net (exploit delivery domain)
cdncounter[.]net
cdn.cdncounter[.]net
count.cdncounter[.]net
sqwas.shapelie[.]com (C2)
141.105.130[.]237 (2025-12-22 to 2026-03-17)
File names
rce_loader.js
rce_module.js
rce_worker_18.4.js
rce_worker_18.6.js
sbx0_main_18.4.js
sbx1_main.js
pe_main.js

